Security
In the age of digital transformation, safeguarding personal and business data is more critical than ever. Whether you're a consumer looking to protect personal information or a business trying to safeguard sensitive customer data, it's essential to have the right security features in place. At [Your Company Name], security is at the heart of everything we do. We are committed to providing top-tier protection, ensuring that you're always safe from potential threats and vulnerabilities. Let us take you through some of the key security features we offer, and why we are the best choice for keeping your valuable information secure.
1. Advanced Encryption Technology
Encryption is a foundational aspect of data security, and we employ state-of-the-art encryption technologies to ensure that your personal and business information remains confidential. Whether you're making an online transaction, sending sensitive documents, or accessing your account, your data is encrypted and unreadable to unauthorized users.
Why It Matters:
- Safe Transactions: All financial transactions are encrypted to protect your financial details and sensitive personal information.
- Data Privacy: Our advanced encryption protocols safeguard your data from cyber threats and hacking attempts.
- Peace of Mind: Perform all online activities, from payments to storing sensitive information, with full confidence in your data’s security.
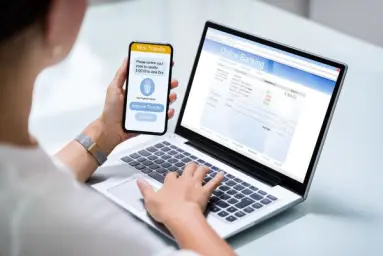
2. Two-Factor Authentication (2FA)
Two-factor authentication adds an additional layer of security to your online accounts. Even if someone manages to obtain your password, they will still need the second factor (e.g., a one-time passcode sent to your phone or an authentication app) to access your account.
Why It Matters:
- Added Protection: Prevent unauthorized access even if login credentials are compromised.
- Easy to Use: Setting up 2FA is simple and doesn’t require technical expertise, providing robust security with minimal effort.
- Extra Security Step: This makes it significantly harder for hackers to break into your accounts.
3. Regular Security Audits
We believe in staying ahead of evolving threats, which is why we conduct routine security audits. These audits help us detect vulnerabilities, fix potential risks, and continuously enhance our security infrastructure.
Why It Matters:
- Proactive Defense: Identify and mitigate weaknesses before they can be exploited.
- Constant Updates: Our team stays on top of the latest security protocols to ensure your protection remains cutting-edge.
- Expert Auditing: Experienced security experts conduct these audits, ensuring that risks are detected and mitigated effectively.
4. Secure Cloud Storage
Our cloud storage solutions are designed with the highest security standards. Your data is encrypted, regularly backed up, and accessible only to authorized users.
Why It Matters:
- Data Redundancy: Your data is backed up on multiple servers, ensuring its safety even if one server fails.
- Scalable Storage: As your data needs grow, our cloud storage scales without compromising on security.
- Access Control: Only authorized users can access your data, and all access is logged for auditing purposes.
5. Anti-Virus and Anti-Malware Protection
We deploy advanced anti-virus and anti-malware software to safeguard your devices and data. These tools continuously scan for threats and neutralize them before they can cause any harm.
Why It Matters:
- Real-Time Threat Detection: Our systems continuously scan for malware, viruses, and other threats.
- Continuous Protection: The anti-virus software receives regular updates to keep up with emerging threats.
- Minimal Impact: Our protection works quietly in the background, ensuring that your systems remain secure without affecting performance.
6. Secure Payment Gateway
All online transactions go through our encrypted payment gateway, which ensures that your financial transactions are secure and protected from fraud or unauthorized access.
Why It Matters:
- Fraud Prevention: Our payment gateway is designed to detect and prevent fraudulent activities, protecting your financial information.
- Quick and Secure Payments: Make payments with the assurance that your financial details are kept safe.
- Wide Compatibility: We offer various payment methods, ensuring you have secure options tailored to your preferences.
7. Robust Firewalls and Intrusion Detection Systems (IDS)
We protect our networks and servers with high-level firewalls and intrusion detection systems (IDS) that constantly monitor for potential threats. These systems act as a proactive defense mechanism, blocking unauthorized access before any damage can be done.
Why It Matters:
- Active Defense: Our firewalls and IDS work tirelessly to detect unusual activity and prevent external threats from reaching your data.
- Real-Time Alerts: Any suspicious activity triggers immediate alerts, allowing us to respond promptly and mitigate risks.
- Safe Networking: Your data is protected during transit, ensuring secure communication and file sharing over the internet.
8. Privacy-First Approach
Your privacy is our top priority. We adhere to stringent privacy protocols and comply with data protection laws such as GDPR to ensure that your personal information is always secure and used responsibly.
Why It Matters:
- Transparency: We are open about how we collect, store, and use your data, empowering you to control your personal information.
- Data Minimization: We only collect the necessary data and use it solely for legitimate purposes, providing you with peace of mind.
- Regulatory Compliance: We comply with international data protection laws to ensure that your data is always handled securely and ethically.
Why Choose Us for Your Security Needs?
Selecting the right partner for your security needs is crucial, and here’s why [Your Company Name] should be your top choice:
-
Comprehensive Security Solutions
We offer a complete range of security features, from advanced encryption to firewalls and secure cloud storage. Your personal and business data is fully protected with our holistic approach. -
Industry-Leading Expertise
With years of experience, we deliver innovative and effective solutions tailored to your specific needs. We stay updated on the latest cyber threats and technological advancements to ensure the best protection. -
Commitment to Privacy
We are dedicated to safeguarding your personal data and adhere to the highest standards of privacy protection. Your financial and personal details remain confidential. -
Reliable Customer Support
Our experienced support team is available to assist you with any security concerns. Whether it’s setting up 2FA or troubleshooting a security issue, we’ve got you covered. -
Continuous Improvement
We believe in constant improvement. Regular security audits and updates keep your protection ahead of the curve, ensuring your data stays safe in an ever-changing digital landscape.
Get Started with Us Today!
By choosing [Your Company Name] as your trusted security partner, you’re ensuring that your personal and business data will be safe and secure. Our robust security features, coupled with our unwavering commitment to privacy, make us the ideal choice for protecting your digital assets. Get in touch today and find out how we can help protect your future!
Related Post
In today’s rapidly changing world, protecting your assets, health, and future is no longer... Learn More
Loans and credit are crucial financial products that help individuals and businesses manage both... Learn More
Mutual funds are one of the most preferred investment vehicles for individuals looking to grow th... Learn More




